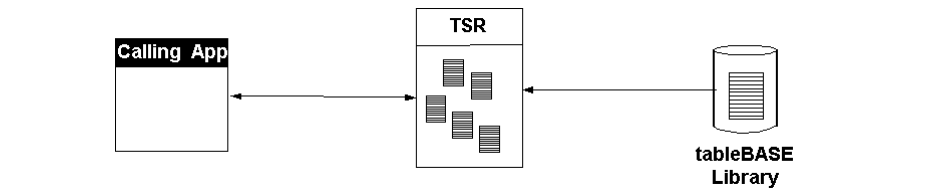
In a typical single-region scenario (see Figure 79), data is sourced from a tableBASE library, into a memory-based TSR. Application(s) within a CICS or IMS region will then access the data in the TSR. Using tableBASE in applications in this way leaves little room for DASD data integrity issues.
However, problems can arise if care is not taken, when multiple CICS regions access data sourced from your library. For example, consider the scenario where three applications load data into their local TSRs from a library (see below). If applications within the top two regions perform only read operations, while applications in the bottom region perform both read and write operations, it is apparent that there can be loss of data integrity. When it shuts down, the library is updated, making it inconsistent with the top two TSRs.
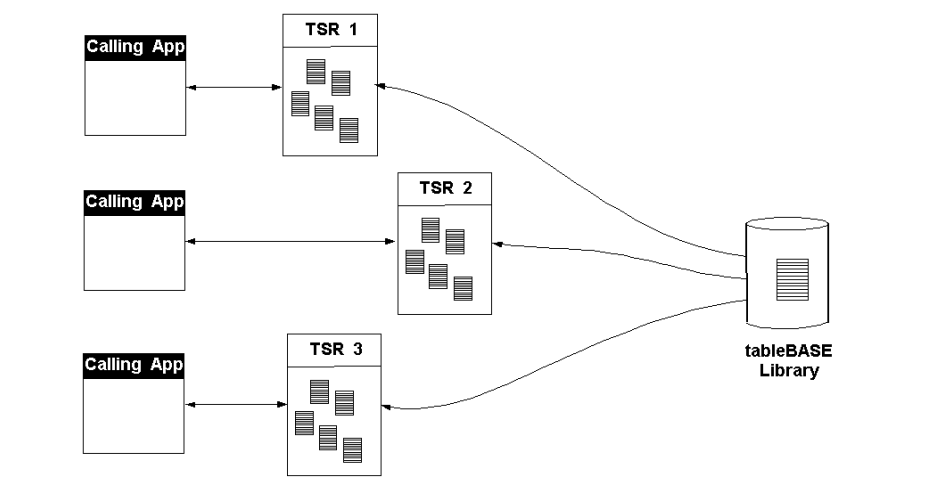
Access control measures can solve the problem, but will very likely impact performance. The more powerful solution is VTS.